In this document, we are going to see the integration process of LDAP and Jenkins. The default installation of Jenkins server uses internal user database which doesn’t work for large development and operations teams. You need to manually create each user.
If you want to access the Jenkins with LDAP credentials (i.e. with Active Directory Credentials), we need to install the LDAP plugin in Jenkins. Jenkins has a native LDAP plugin which can be used to authenticate users against an external LDAP server, such as OpenLDAP etc. So, please make sure to install LDAP plugin in Jenkins before configuring the setup.

Steps: –
The following are the steps to configure the LDAP – Jenkins setup.
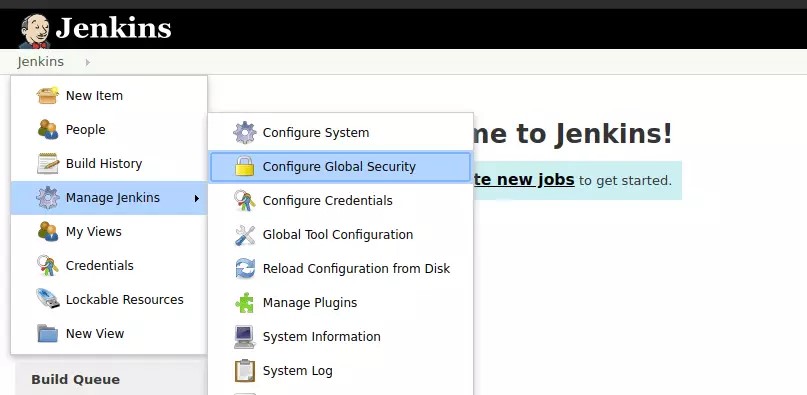
- In order to configure the LDAP – Jenkins setup, some parameter values are needed and need to be filled in. But before that, we need to login into Jenkins server as admin user and navigate to ‘Jenkins > Configure Global Security “.
2. Select ‘LDAP’ under ‘Access Control’ and then enter the LDAP server details and press ‘Save’ button. Please fill out the parameters by providing the details of the image below.
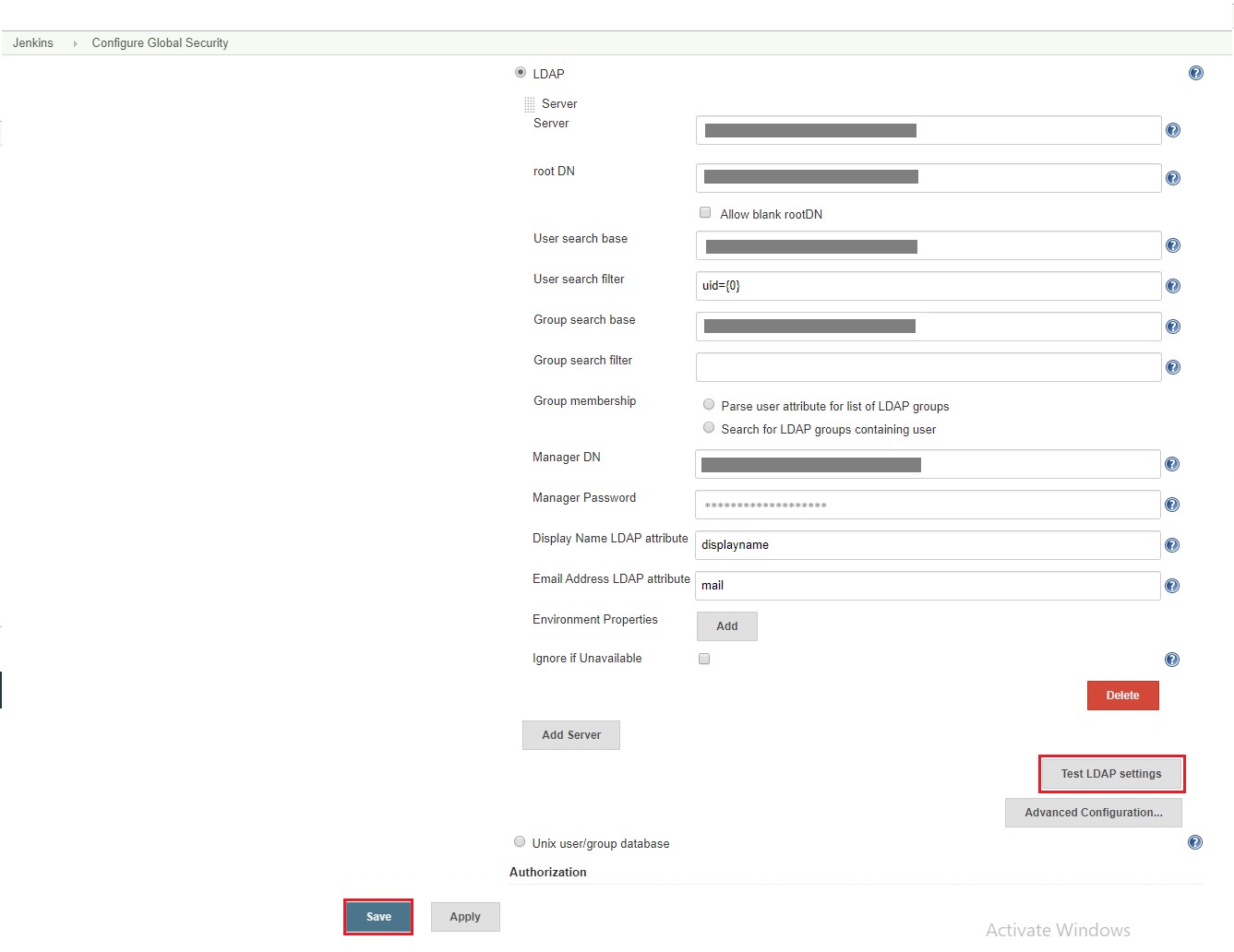
3. Test the connection establishment after configuring LDAP by pressing the ‘Test LDAP settings’ button.
4. After the connection is established, basic authentication will be available. Users can then login using their directory credentials from Jenkins login page.
Conclusion: –
We should have configured Jenkins server successfully to aaaauthenticate user via LDAP Server. Please notice that we can not sign in with Jenkins database users once LDAP authentication is enabled because Jenkins local internal user database is disabled. Both cannot coexist, for some reason.
